Autonomously enforce data access and activity governance to meet compliance and security mandates.

F1000 Healthcare
With massive growth in data and cloud migration, collaboration and sharing have never been easier. On the other hand, data discovery and risk assessment are becoming even more difficult.
Controlling information flows between departments and third parties is essential to meet regulatory mandates and protect sensitive data from disclosure or a data breach.
All organizations, especially regulated enterprises, have obligations to strictly control employee access to private, sensitive data. Many other corporate activities – such as mergers and acquisitions – also need robust internal information barriers.
Unfortunately, sensitive data is often embedded in hard-to-find and hard-to-manage places like financial analysis spreadsheets or business forecast reports.
Data access governance (DAG) is the process of defining and enforcing policies for how data is accessed and used. It includes defining roles and responsibilities for those who have access to data, setting up processes for granting and revoking access, and auditing data access.
Data access governance may also include risk assessments, privacy policy implementation, deploying access controls, discovering and classifying sensitive data, and monitoring access to critical assets.
Improve security and compliance while limiting risk of regulatory fines
Know how your data is being used, where it’s located and whether it’s at risk
Enable employees with access to relevant data that explicitly applies to their role
As the remote and hybrid work model continues to dominate how employees work and promote more data-driven operations, compliance regulations become more crucial. With data access governance, organizations can improve security and compliance while limiting their risk of regulatory fines.
Concentric’s powerful deep learning technology improves data access and activity governance by giving you an unparalleled contextual understanding of your structured and unstructured data. Our solution helps remediate data vulnerability issues, meet access and activity governance regulations, demonstrate control to auditors, and implement zero–trust access practices – all without complex rules or relying on end-users.
Sensitive data is often embedded in hard-to-find and hard-to-manage places like financial analysis spreadsheets or business forecast reports.
Organizations must find, assess, and control business-critical information to build effective information barriers between internal groups. Our rule-free Risk Distance analysis engine comprehensively identifies data that may be at risk from inappropriate classification, permissions, entitlements and sharing — including link sharing, sharing with third parties, personal email addresses, or risky sharing within your company.
Skyrocketing cloud migration, more employees working from home (WFH), and corporate Bring Your Own device (BYOD) initiatives are all contributing to more data to manage than ever before. Managing this access presents a significant hurdle, as they must be diligent about protecting these streams of information.
Concentric helps you meet access and activity governance regulations, demonstrate control to auditors and implement zero–trust access practices. Plus, our solution’s easy, autonomous remediation fixes access issues and reduces odds of data loss or governance violation.
Yes, our solution connects to on-premises unstructured data storage, structured databases, messaging and email applications. That means Concentric can discover, categorize and monitor data wherever you’ve stored it.
The solution uses sophisticated machine learning technologies to autonomously scan and categorize documents. The MIND™ deep learning- as-a-service functionality means you will always have the latest AI models for fast, accurate discovery and categorization.
In today’s business landscape where digital transformation has almost reached ubiquity, data has become the backbone of almost every business. ...
As the transformation towards digital and cloud continues its rapid pace, data is becoming one of the most valuable assets...
What is SOX? The Sarbanes-Oxley Act (SOX) of 2002, a U.S. federal legislation, was created to protect investors by increasing...

Libero nibh at ultrices torquent litora dictum porta info [email protected]
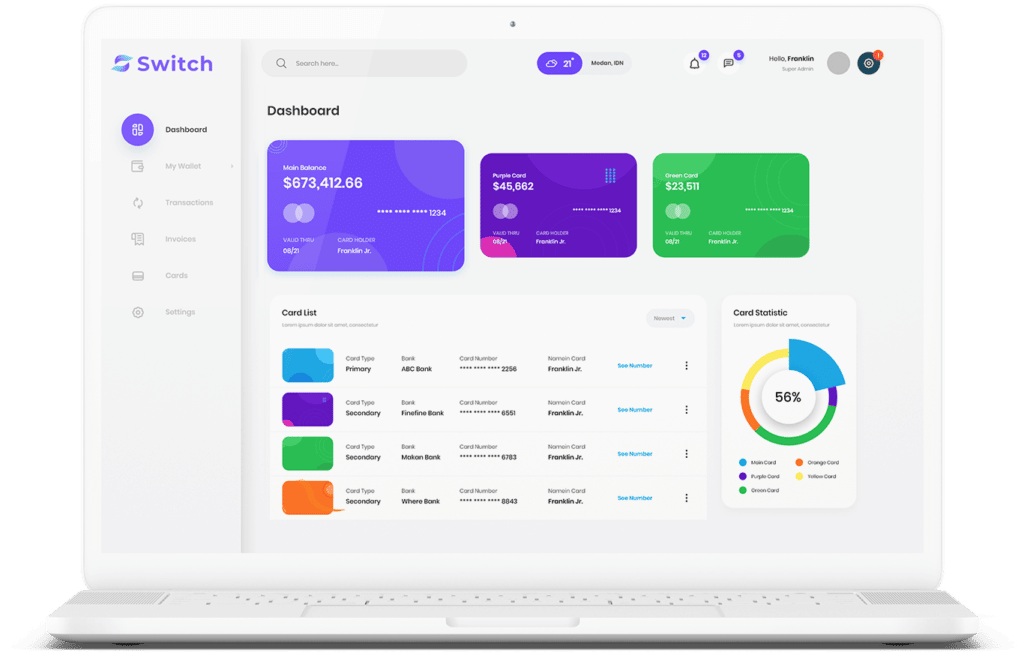
Start connecting your payment with Switch App.