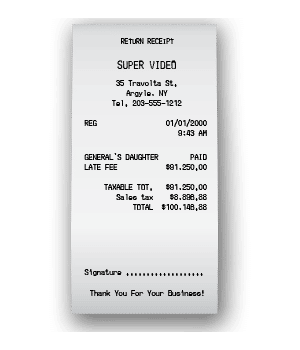
A customer in upstate New York, returning a copy of “The General’s Daughter” on the first day of 2000, faced an astonishing $91,250 late fee. According to the computer at his local Super Video rental store, the tape had been out for more than 100 years.
Fortunately for the rest of us, that was the worst of the feared Y2K disaster. After more than a decade of preparation and $100B worth of work, the IT community fixed what’s been described as the most expensive software bug in history. Airplanes stayed aloft, electricity stayed on and life carried on as usual.
Which goes to show a couple of enduring IT truths. First, planning matters. Y2K wasn’t the disaster we feared not because it wasn’t real but because it was anticipated. And second, even with a good plan, you just never can tell – as a laughable late fee showed us then and a distinctly unfunny pandemic reminds us now.
The “bring your own” genie will leave the bottle
Over the last decade, authority for every productivity-related technology decision has inexorably moved away from IT professionals to the users and lines of business closest to those decisions. The first phase of this trend, “bring your own device,” is essentially over. It’s nearly impossible to imagine a return to corporate-controlled Blackberries without also imagining a large-scale employee revolt.
Last year, work-from-home practices increasingly put line employees in charge of data access and management decisions. And it goes without saying that in 2020 this trend broadened exponentially. Cloud storage and productivity applications maximize online productivity by making collaboration easy from anywhere. But while link sharing may be liberating, the data security ramifications lend the trend a darker edge that’s hard for security professionals to control.
Next year, the BYO trend will continue as line of business teams will further claim the authority to choose as-a-service solutions without IT involvement. Functionally specialized online services are now as capable as their on-premises predecessors, they’re easier to stand up, and they’re cheaper to own. Call it “bring your own SaaS” if you’d like, but you can expect, as an example, the accounting department to pick (and maybe implement) the online invoicing solution they like without much consultation with the IT team.
Data privacy goes in unexpected directions
After a few years of relative predictability, data privacy promises to get more “interesting” in 2021. The GDPR and CCPA regulatory regimes each notched milestones in 2020. The GDPR (as of this writing) had assessed a record level of fines totaling €220 million. California’s CCPA enforcement kicked in on July 1st, and voters in that state passed additional privacy restrictions via a November ballot initiative (the California Consumer Privacy Act or “CRPA”). The CRPA extends and modifies the CCPA, with new mandates taking effect at the end of 2022.
Here’s where things are going to get interesting. Optimistically, effective COVID-19 vaccines will facilitate the ability for in-person work by mid-year. But it’s just as likely delays in distribution, reluctance to inoculate and lingering stress on the healthcare system will extend work-from-home practices for many through 2021. Either way, organizations will face obligations and temptations to collect more data on their employees – about their immunization status, health situation, work habits, even their social interaction patterns – than ever before.
Today, most practitioners focus on risks from external threat actors. But with a bracing action in October, the GDPR authority showed they’re equally concerned with human resources data when they slapped clothing retailer H&M with a €35 million fine for illegal employee surveillance. Regulations governing employee data management are currently more forgiving in the US. The CCPA, for example, includes a so-called HR exception (which exempts internal employee information from the regulation) that’s set to expire at the end of 2023. But regardless of the go-live date, privacy protections for employee data are clearly in the cards.
Strategic Response
There’s no way to predict every 2021 eventuality. But we can forecast at least two key trends:
What’s the right path forward? Your strategic data security plan in 2021 (and beyond) should follow this simple guiding principal: Apply zero-trust security principles to data wherever it’s stored and used. In an uncertain regulatory and threat environment, zero trust (which protects data by limiting access to only those with a need), is the ideal policy approach. The devil is, as they say, in the details.
In 2021, those details will increasingly be met by AI-enabled data discovery and risk assessment tools that can automate zero-trust security. Vendors commercializing some of the most promising deep learning research can now autonomously categorize data, assess business criticality, and even deduce appropriate data management policies – all without extra IT overhead, rule development or end user help.
Planning matters. A hefty dose of uncertainty is certain to await us in 2021. And whatever may be in store for us next year, we can take steps now to anticipate the data security trends that’ll shape IT in 2021 and beyond.
An edited version of this post appears in VMBlog.