Knowing where all your data resides is like playing a game of hide and seek with no boundaries or rules. Data is ubiquitous, residing in …
For organizations today, achieving robust data governance, compliance, and security across their expansive data landscapes is much easier said than done. But with the right …
Customer Relationship Management (CRM) systems like Salesforce are critical business software tools and have reached a new level of SaaS ubiquity. However, CRMs store critical …
Note: this article has been updated and refreshed as of 7/17/24 As the cybersecurity landscape evolves in scope and complexity, encryption remains a key layer …
Data is the backbone of the modern organization. Today, organizations generate, process, store, and manage more data than ever before. As the volume of data …
Cloud computing has revolutionized the way organizations store, process and share data. But with this transformation come new security risks. With massive cloud migration and …

Libero nibh at ultrices torquent litora dictum porta info [email protected]
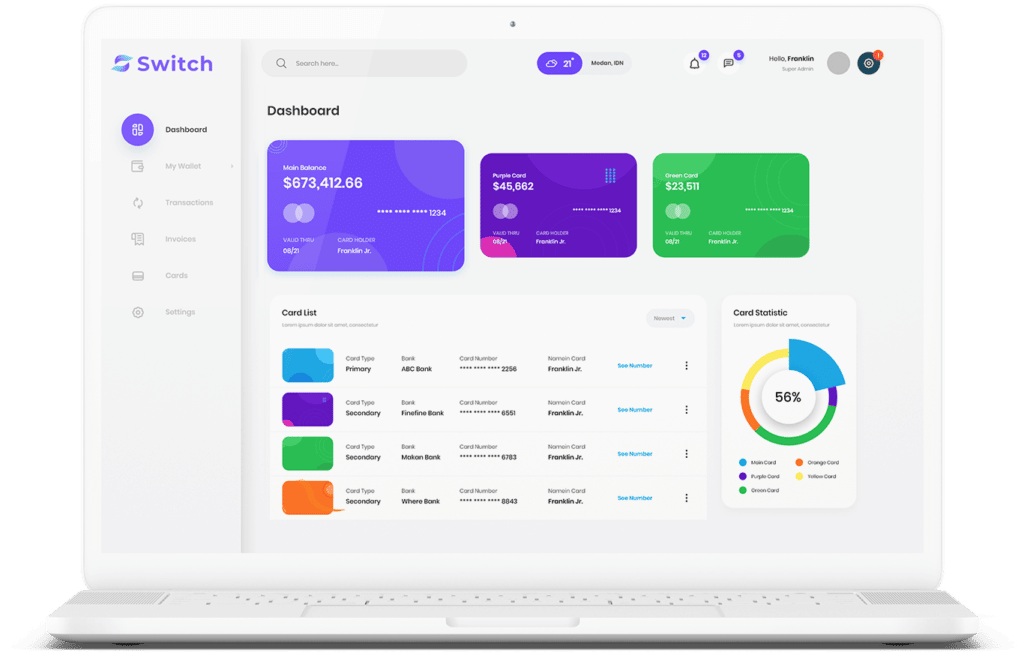
Start connecting your payment with Switch App.