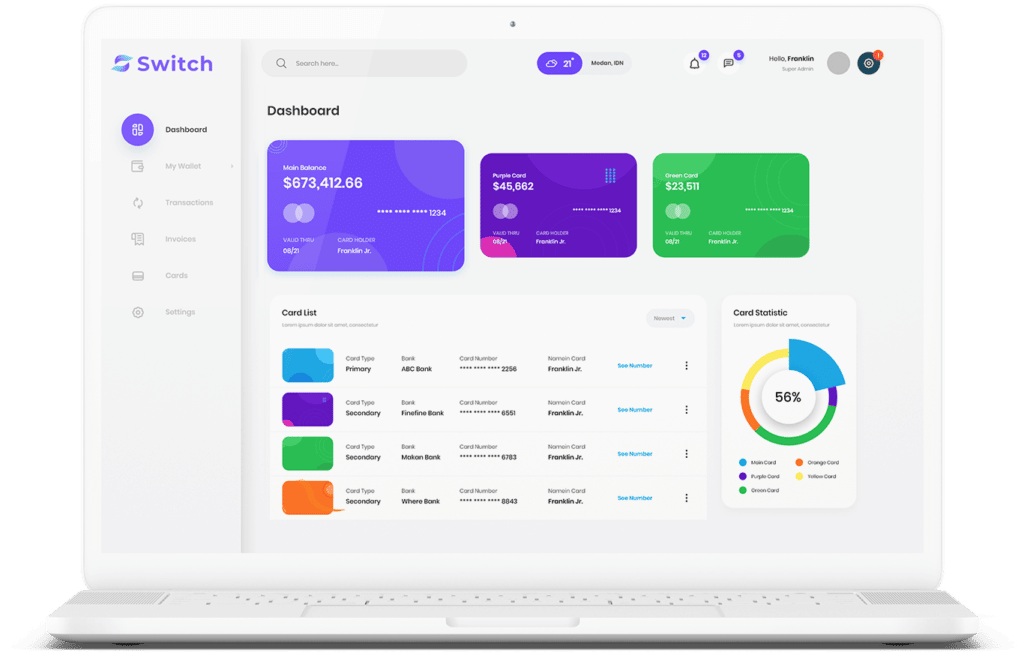
Our natural language processing (NLP) capabilities far exceed the pattern or keyword-based techniques of other automated approaches and solutions. Concentric’s NLP can, for example, interpret the meaning of the same word used in different contexts or interpret the meaning of an entire sentence or paragraph to accurately understand the semantic context of data.
The Concentric MIND service catalogs and curates deep learning models to ensure you always have the latest and best-fitting solution for your data. Sophisticated peer file analysis maximizes classification accuracy.