Note: this article was updated and refreshed as of 4/1/24. If you’ve used ChatGPT, you know how powerful and helpful it can be. For the …
Have you ever considered the invisible barriers that exist within your organization? With so much data flowing in more places than ever before, it’s essential …
In a business landscape dominated by rapid digital transformation and AI adoption, protecting all information — even data generated by AI — has never been …
As data security moves up the priority list of almost every boardroom, picking the right solution is as important as the data that requires protection. …
As artificial intelligence continues to dominate discussions about its role in the workplace, Google’s introduction of Gemini (formerly Bard) will surely be another hot talking …
As cloud adoption skyrockets alongside the surge in the sheer amount of data organizations share, managing access to that data can be overwhelming. While cloud …

Libero nibh at ultrices torquent litora dictum porta info [email protected]
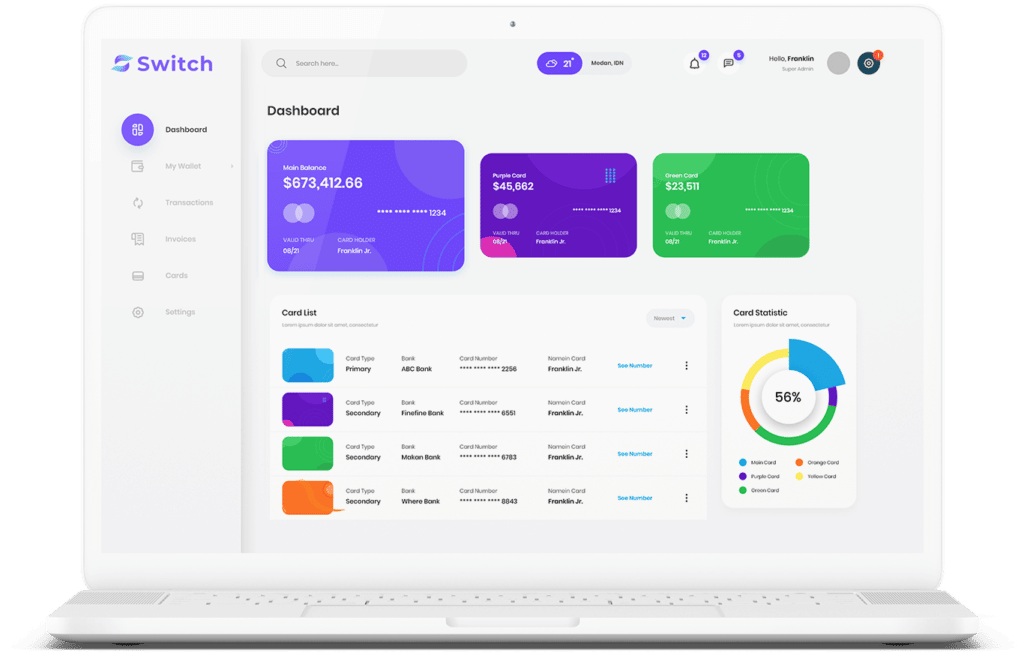
Start connecting your payment with Switch App.