In the New Testament, the Four Horsemen are punishments from God, and their arrival signals the end times. Ransomware victims, facing cyber adversaries who take down critical infrastructure, hospitals, schools, and cities without qualm or quarter, might be forgiven for feeling that the end times have, in fact, arrived.
Of course, they haven’t, but the sinking feeling that ransomware changes the game isn’t just unwarranted paranoia. We may not face an actual apocalypse, but we do confront new IT dynamics and novel attack techniques that force us to rethink cybersecurity. Here are the Four Horsemen of the ransomware “apocalypse”:
Despite our best efforts, and after making significant investments in technology and training, it’s clear we can’t wring human gullibility out of the system. It’s a fool’s errand to think we can protect users from themselves. While phishing and deceptive malware were around long before ransomware, account takeovers via social engineering are essential for many ransomware attacks.
These takeovers make encryption of the user’s files possible while also giving perpetrators a toehold as they work to extend attacks to more systems and data. Depending on what the compromised account can access, that toehold has the potential to devastate organizations that haven’t rigorously limited access to only necessary systems and data.
Resisting the Gullibility Horseman requires systematic and rigorous attention to least-privileges access control for resources and data. Eliminating human gullibility is not an option – but limiting the damage caused by an account breach is. Concentric’s Risk Distance™ analysis can identify overshared data so you can enjoy the benefits of consistent, autonomous data access governance.
For well over four decades, security professionals prepared for cyberthreats as they might for a bank heist: like money in a vault, data was safe if it stayed put. In the old days, stopping data movement stopped data loss. That, of course, led to the defenses that are data security’s equivalent to guards at a bank. Firewalls and data-loss prevention solutions stand watch at the perimeter, keeping data in and bad guys out.
Ransomware makes it possible to rob a bank without ever moving the money. It’s a fiendishly simple mechanism: encryption can make data inaccessible without any data movement at all. (Although a combined data theft/encryption attack gives attackers additional extortion options – and these multi-front attacks are increasingly common.) This has profound implications for existing security measures. The perimeter no longer demarcates “protected” from “lost” since ransomware can bypass many traditional defenses.
Combatting the Stealth Horseman demands vigilance across your entire IT environment. Legitimate encryption activities are both ordinary and necessary, which means your defenses must understand what’s been impacted by unwanted encryption. That’s a tall order, but Concentric’s content-aware ransomware solution does just that.
Cryptocurrencies are the most modern of our four horsemen, but conceptually they have deep historical roots. Anonymous financial transactions, a la the notorious Swiss banking system, have long been associated with drug lords, tax cheats, and kleptocracies. That ransomware perpetrators should embrace Bitcoin comes as no surprise.
Modern technology takes the friction out of financial anonymity. Establishing a cryptocurrency account doesn’t require a trip to Zurich, and redeeming and using crypto is a simple, straightforward, and internationally available process. With apologies to the vast majority of legal Bitcoin owners, there’s no question cryptocurrencies are one of the Four Horsemen of the ransomware apocalypse.
And there’s not much you, as an IT security professional, can do about it. Unless, of course, you can build a time machine, skip back to 2007, buy a few thousand Bitcoin, and retire.
According to Coveware, most ransomware attacks target small to mid-sized businesses. The reasons, unfortunately, relate to funding: smaller companies often can’t afford expensive email filtering software or comprehensive employee training. One heartbreaking example targeted Vastaamo, a Finnish mental health provider network with a modest IT budget and thousands of sensitive clinical records. “Ransom_man,” as the perpetrator called himself, demanded payment from Vastaamo while also extorting individual patients with threats to release their private therapist records.
It’s a complicated story, and poverty is only a part of the problem that led to Vastaamo’s compromise. But as a cautionary tale, it illustrates the depths cybercriminals are willing to go in their quest for ransom. Avoiding cybersecurity investments is Russian roulette – especially if you’re a smaller organization managing sensitive data.
Concentric’s leading content awareness capabilities, combined with our new ransomware solution, help organizations prepare for, detect, and analyze attacks. With Concentric, you’ll have the tools to harden your IT systems, spot unwanted encryption, and investigate breaches faster and more accurately than ever before.
Sound interesting? Get in touch – we’d be happy to set up a demo!
Note: this article has been updated and refreshed as of 7/17/24 As the cybersecurity landscape evolves in scope and complexity,...
Data is the backbone of the modern organization. Today, organizations generate, process, store, and manage more data than ever before....
It’s time again to talk about ransomware. We know it’s still happening, but as hard as we try, we can’t...
Have you ever considered the invisible barriers that exist within your organization? With so much data flowing in more places...
Not long ago, the term data privacy was considered a buzzword. Today, data privacy has moved to the forefront of...
Almost every IT project must, at some point, run the financial justification gauntlet. Even initiatives with broad organizational support, like...

Libero nibh at ultrices torquent litora dictum porta info [email protected]
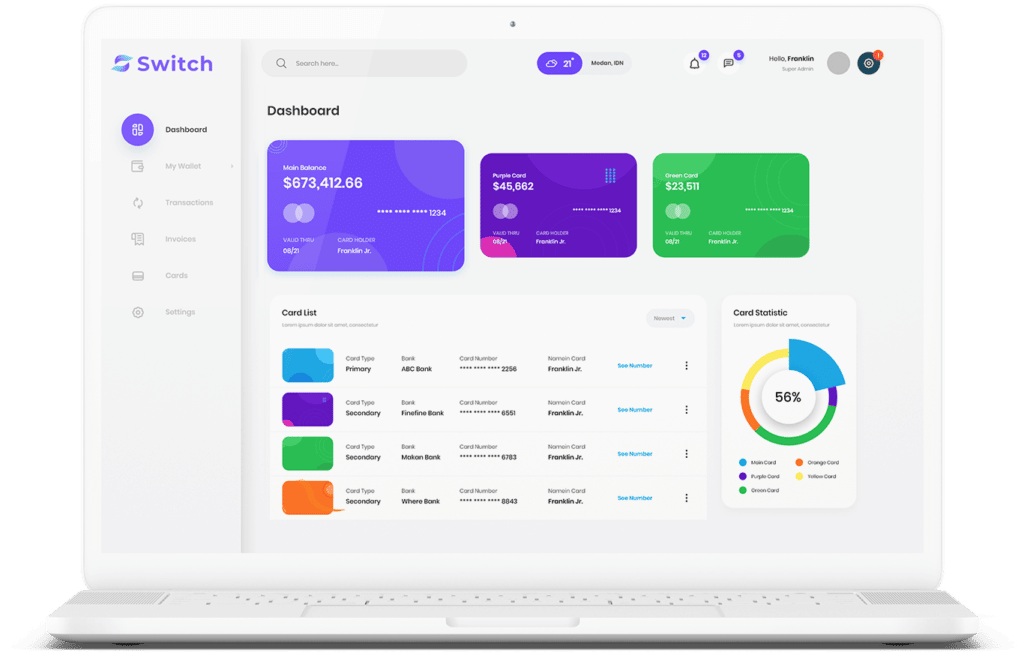
Start connecting your payment with Switch App.