Content-Centric Security Across Cloud and On-Premises Data
5 Best Practices for Security in Mixed Cloud/On-Premises Environments
• Consolidate data access governance
• Focus on at-risk content
• Don't rely on end users
• Proactively remediate risk
• Embrace automation to optimize staffing
Managing Multiple Data Stores?
When you have terabytes or even petabytes of data under management, access governance – especially across multiple on-premises and cloud data stores – is a significant challenge.
Do you need to find data across SQL databases and cloud stores?

What's Important?
Data sprawl fatigue is real, and it can be the weakest link in an otherwise robust security architecture. When IT security professionals have too many signals to investigate, risk falls through the cracks.
Concentric finds the critical content you need to protect. Our deep learning-based data discovery lets you zero in on important, at-risk content so you can focus on solving problems, not chasing false alarms.
Want to know how it works?
Protection Without Frustration
It’s tempting to ask end users to manage access permissions for the files they own. But we know from experience it doesn’t work. End users, after all, have a day job.
With Semantic Intelligence™, you’ll accurately and autonomously manage permissions and data classification, which translates to lower risk, better coverage, and happier end users.
Wondering how it works in the real world?

It's More Than Compliance
Delivering regulatory compliance is one of the security team’s key responsibilities. But compliance is only part of the story. Proactive risk mitigation that goes beyond compliance is how to keep your organization out of the headlines.
Concentric does more than just discover content and identify risk. Our embedded tools make remediation a breeze, and we improve your existing security stack with a variety of integrated services.
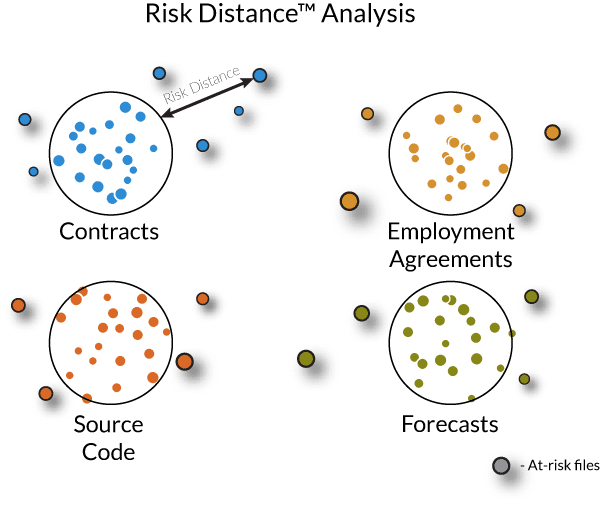
Automation, the Force Multiplier
Security staff in short supply? You’re not alone. Cloud data security automation is the answer.
Our Risk Distance™ analysis technology takes labor and guesswork out of the equation. By comparing security practices for one file to similar data, we can give you insights without an army of security analysts.
Want to see how it works?
Powerful AI Technologies
Simplify Cloud/On-Premises Data Security
Automated Data Discovery
Our deep learning engine gives you a content-centric perspective.
- Powerful natural language processing technology for accuracy and efficiency
- Manage data access based on the meaning of the content, not the location of the file
- Find and protect mislocated, overlooked, or legacy data
Risk Remediation
- No rules or regex required
- Benefit from the expertise of content owners without wasting their time
- Prevent oversharing, third-party access, wrong location, misclassification and more
Zero Trust/Zero Touch Data Security
- Comply with insider access regulations and best practices
- Analyze hard-to-find access caused by cascading group permissions
- Securely off-board employees and implement zero-trust governance
Let's Get Started!
Get Concentric's free risk assessment report for cloud/on-premises storage environments
- Designed for dispersed, multi-cloud and on-premises environments
- Meet regulatory compliance requirements
- Integrate with your existing security stack
- Discover and categorize content - wherever it's stored
Demos
Learn About Semantic Intelligence™

Join Karthik Krishnan, Concentric AI CEO, talks AI with Stephen Foskett and Chris Grundemann from Gestalt IT


See how Semantic Intelligence can discover data and govern access to content without rules or regex