Data Detection and Response (DDR) is a cybersecurity solution that protects cloud-based data against potential threats, breaches and exfiltration. Think of it this way: traditional security measures focus on securing the infrastructure or perimeter, but DDR puts the emphasis on the data itself.
DDR, by definition, is about real-time monitoring, detection, and response. It provides a layer of dynamic monitoring on top of the static defense layers offered by Cloud Security Posture Management (CSPM) and Data Security Posture Management (DSPM) tools.
DDR solutions work by using real-time log analytics to monitor cloud environments that store data and can detect data risks as soon as they occur. Once sensitive data sources have been mapped, the DDR solution starts monitoring activity related to these assets.
DDR then parses the log in near-real time and applies a threat model to identify suspicious activity, such as data flowing to an external account. The event or activity is assessed against the threat model, and if a new risk is found, the DDR will issue an alert and suggest the best response.
DDR’s threat model is a key component here. These models are developed by cybersecurity researchers and take into account attack patterns established in previous data breaches, the specific weaknesses in each data service, and how bad actors can exploit them.
Think of DDR, DSPM (Data Security Posture Management), and CSPM (Cloud Security Posture Management) as the three-piece band of cloud security protection. Each member of the trio plays a different instrument and offers its own specific cybersecurity talents.
CSPM tools are designed to manage the security posture of a cloud environment. They provide visibility into the cloud infrastructure and help identify misconfigurations or compliance violations. But CSPM is static in nature and emphasizes the infrastructure rather than the data.
DSPM tools, on the other hand, focus on the data itself. DSPM helps organizations understand where their sensitive data is, who has access to it, and how it’s being used. DSPM tools can identify data that’s at risk and provide alerts for potential security violations. Like CSPM, DSPM is still somewhat static and focuses on the data’s posture rather than real-time events.
DDR is a more dynamic solution that complements CSPM and DSPM. While CSPM and DSPM provide a static defense layer, DDR focuses on real-time data events. It monitors data activity as it happens, detects potential risks, and provides alerts and suggestions for response – giving security teams a chance to intervene before damage is done.
DDR provides mission-critical functionality that is often missing from existing cloud security stacks. It protects data from being exfiltrated or misused and may prevent compliance rule violations.
Here are the key benefits of DDR:
Real-Time Monitoring and Response: DDR enables immediate detection and response to potential data-related risks in real-time.
Enhanced Data Protection: By focusing on data activity, DDR provides an additional layer of protection against data loss or exfiltration.
Complements Existing Security Measures: DDR adds a dynamic layer of protection to the static defense provided by CSPM and DSPM tools.
Reduces Operational Overhead: By integrating with existing SIEM/SOAR solutions, DDR allows for efficient management of all security alerts in one place.
Proactive Threat Mitigation: DDR uses advanced threat models to proactively identify and respond to potential data threats.
Compliance Assurance: DDR helps maintain regulatory compliance by detecting potential violations and enabling prompt remediation.
In today’s complex and multi-cloud environments, DDR can help security teams catch incidents earlier, averting disastrous data loss or minimizing the damage it causes.
Concentric AI’s Data Security Posture Management solution offers all the DDR benefits while providing visibility into the who, where, and how of your sensitive data. It identifies all the sensitive data in the cloud, from intellectual property to financial to PII/PCI/PHI, without burdening security teams to craft rules or complex policies.
Concentric AI establishes what data is being shared with whom – internal users/groups or external third parties. It tracks data lineage as it moves across your environment, providing a clear view of data access and movement.
This detection capability is crucial for maintaining a robust data security posture.
Data Detection
Concentric AI identifies where the data may be at risk — typically sensitive data that is not being shared in accordance with corporate security guidelines and where access or activity violations are happening quickly. With Concentric AI, you’ll know where your sensitive data is across unstructured or structured data repositories, email/messaging applications, cloud or on-premises – all with semantic context.
Best of all, our solution helps you discover and remediate risk without writing a single rule. It identifies data that may be at risk from inappropriate classification, permissions, entitlements, and sharing.
Incident Response
Concentric remediates issues as they are happening, such as fixing access control issues and permissions or disabling third-party data sharing for a sensitive file that should not be shared. Our solution can compare semantically similar data for classification mismatches, end-user errors or malicious insiders, identify anomalies, and easily remediate these issues.
Essentially, Concentric remediates potential threats before they become serious problems. Plus, your SOC analysts get actionable insights to help with response efforts.
In addition, Concentric can help with incident response use cases from employee offboarding to data breach investigations by providing deep context into the who , where and how of data access and activity
Forensics and Understanding Data Risk
One of the key strengths of Concentric AI lies in the ability to perform digital forensics by understanding where the data is and its inherent risk. By identifying all sensitive cloud data, whether it’s structured or unstructured, Concentric AI provides a comprehensive view of an organization’s data landscape. This level of visibility is crucial in understanding the cybersecurity risk to systems, assets, data, and capabilities.
Concentric AI’s advanced deep learning technology compares each data element against baseline security practices used by similar datasets. This process allows the system to identify where the data may be at risk, such as sensitive data not being shared in accordance with corporate security guidelines or where access or activity violations are happening quickly.
Rapid Data Recovery in the Event of Ransomware
In the face of a ransomware attack, every second counts. Rapid recovery is crucial. By maintaining a clear understanding of data’s location and lineage, Concentric AI can help organizations quickly identify the affected data and initiate recovery processes. With such rapid response, businesses can significantly reduce downtime and the associated costs of a ransomware attack.
Preventing Data Exfiltration
Data exfiltration poses a significant threat to organizations, especially when it comes to events like employee offboarding. Concentric AI helps to mitigate this risk by monitoring data access and sharing. It establishes what data is being shared with whom – whether it’s internal users/groups or external third parties – and tracks data lineage as it moves across the environment.
In the event of abnormal data movement or access patterns, Concentric AI can issue alerts and take remedial action, such as fixing access control issues and permissions or disabling third-party data sharing for a sensitive file that should not be shared. This proactive approach helps to prevent data exfiltration before it occurs, safeguarding the organization’s sensitive information.
With Concentric, your organization can:
Our solution provides agentless integration with numerous cloud products and services.
It’s also so easy to deploy — sign up in 10 minutes and see value in days.
With massive cloud migration and more data being stored and collected than we ever imagined, protecting that data is mission-critical...
Cyberattacks targeted at big-name businesses may take up most of the headlines, but cybersecurity incidents are also on the rise...
Massive cloud migration and digital transformation are inarguably great for business, but managing all that data is like fighting a...
As cloud migration and digital transformation continue influencing IT operations, data is everywhere, and threats are evolving at an alarming...
It seems like it happens almost every day: a confidential data breach appears in the headlines. The damages are getting worse...
In today’s business landscape, in which data is proliferating at an unprecedented rate, organizations are looking for innovative solutions to...

Libero nibh at ultrices torquent litora dictum porta info [email protected]
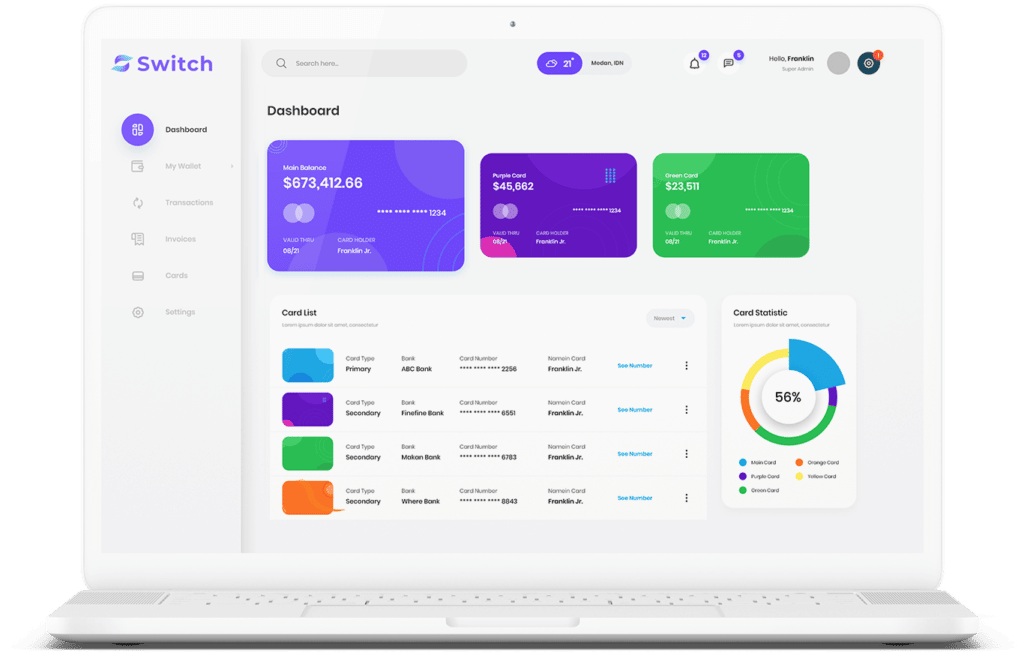
Start connecting your payment with Switch App.